Anthony Watts runs the excellent award-winning climate website Watts Up With That
Over the years, he alluded to some hearing problems but never dwelled on it. Today, he posted a wonderful story about how he has now regained almost all of his hearing. Something to forward to anyone you know with hearing problems. A great read.
From Anthony:
How I got my life back – my hearing has been restored to near-normal
This is an extremely personal note, and I have been waiting a week to write to see if in fact the results were real and lasting. I’m happy to report that they are and I am a changed person as a result of this transformation. Let me tell you a story about my struggle and how I suffered with for years now my family and my friends in my career and everything suffered along with it and what I did to solve it.
Many of you that read WUWT and have met me in person at conferences, speaking engagements, and over the telephone realize what a struggle everyday life has been for me with an 85% hearing loss. The story begins when I was an infant – I had a series of infections which our local doctor treated with tetracycline, an antibiotic that at the time they did not know would cause long-term hearing loss. It also causes discoloring of your adult teeth in later life. Like with so many drugs, no one quite knew at the time what long-term effects it might have. The product is now [mostly] off the market, however the effect remained with me and many other people.
Anthony finds a clinic that deals with his problem:
This section of the campus at the Starkey Laboratories is called the Center for Excellence and indeed it is, because this is where miracles are performed every day by a staff of caring and talented people that exist nowhere else in the world.
The walls are lined with photographs, autographs, and letters from heads of state, celebrities, astronauts, the Pope, and even a letter from Mother Teresa thanking the man that formed this company and the miracle that it produces for restoring their hearing.
And the results are excellent in even the worst conditions (lots of ambient noise and other people talking):
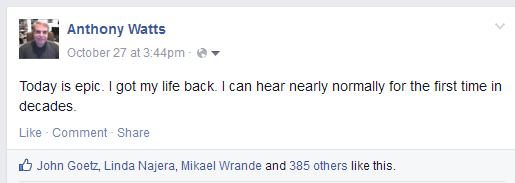
This was a moment I’ll remember forever. All of a sudden the tables were turned, and I was thrilled beyond imagination to be able to repeat something for someone else. I knew then that a transformation that occurred and I made it short and simple post to my Facebook page. It read:
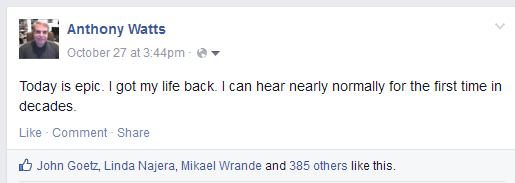
And to my amazement dozens and then hundreds of accolades and comment started pouring in while I was sitting there at the bar. I began to cry and tears were streaming down my face. I was so happy and I couldn’t stop it because the weight and pain of the last 40 years were suddenly lifted from me. It truly was epic.
There were two people sitting at the end corner of the bar who looked at me and asked with concern, “Sir, are you okay?” I proceeded to tell them what happened and I had a glorious conversation with two people who I had never met and I understood every word. They were thrilled for me.
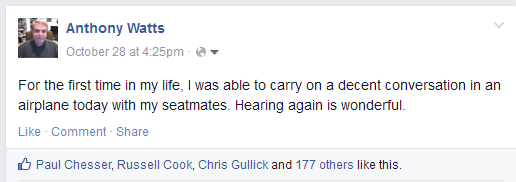
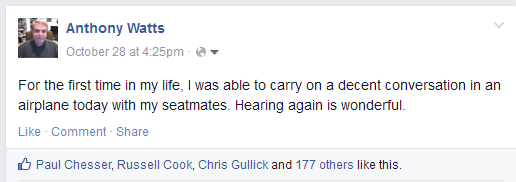
I can’t begin to tell you what that felt like. And it kept getting better as I learned to be able to tune these new hearing aids to situations and it made comprehension even easier. The next day I posted this on my Facebook page:
I had feared that maybe this was just the temporary gain, but now nearly a week later my comprehension gains continue, and I am healed in more ways than one.
You see, the inability to hear on a daily basis during normal simple everyday things like ordering a cup of coffee at Starbucks or going through a drive through the order food to take on the my family were challenges that I often failed and it made me frustrated and angry all the time. This affected people around me and especially the people I hold most dear; my own family. Now all of that is gone and I’m like an entirely new person because of this transformation.
My ability to hear and the telephone has been transformed too. These new hearing aids have direct Bluetooth connections and so I am able to carry on a conversation using both ears with my cell phone. The fidelity is phenomenal and my comprehension is now nearly perfect where maybe before I could pick up 50% on a good day. This new technology is beyond what I could have imagined.
The place that Anthony went to is the Starkey Hearing Foundation - amazing people, amazing work.